Key Highlights
- What is a mobile identity?
- How does mobile identity create a secure user experience?
- Use Cases & problems while using mobile authentication & how it can be tackled.
- Attributes of mobile Identity.
In today’s world mobile-first approach ensures delivering the right user experience to the focused users. According to a recent study done by the Digital Information World, adults spend more than 6 hours on average surfing on the internet. Even every service provider wants the authenticity of the user as it is exposed to its vulnerability where people try doing frauds to service providers.
The world is shifting from web-based business to mobile app-centric. It’s a smarter way to use mobile identity as it identifies users using their sim card. It also helps in giving header enrichment by providing secured customer identity as sometimes email is not the strong primary identity on mobile. Even the data which is collected from devices may not be secured creating havoc and may lead to hacking of apps, devices can be rooted, also malware mobile devices.
When users use the fake number or landline number, VOIP numbers, one-time burner phone numbers which become difficult to get authenticated users but it can be tackled by using mobile identity by ensuring better reachability & reducing frauds. Sometimes it happens that we receive our SMS, OTP’s a little late or is forgotten by us so we go back to remembering the code but using mobile identity it does the SIM identification ensuring a frictionless & quick transaction.
Due to the increased cross border digital and mobile fraud, executives are under pressure to reduce risks escalating these frauds. However, businesses need to understand that there is no one size fits all solution, a layered solution approach that involves identity authentication, transaction verification, and other digital identity tools to fight fraud can be impactful in fighting fraud without impacting user experience and growth.
The silent verification:
It verifies the end-users’ mobile phone number effortlessly in the background while they indulge in the entire experience, ensuring that one is dealing with the same user.
Personal data verification:
It authenticates the customers and verifies their personal information by comparing it with the most recent records held by mobile operators.
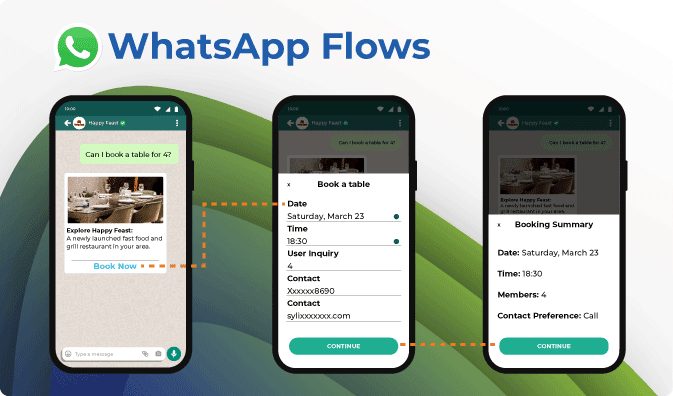
Automated Form Filling:
The form filling process is shortened from minutes to a couple of seconds. The details get mapped at the backend. It takes less than 10 seconds. The automated form filling with verified and recent user information ensures instant customer onboarding, minimal cart abandonment and reduced time to fill the form.
Fraud Protection:
It prevents Account Takeovers (ATOs) as it monitors account, network and device changes from returning users in real-time, as well as chargeback/bust outs. It has multi-modal identity proofing, low onboarding costs and provides real-time decisions for high-value transactions. It offers real-time trusted data directly from mobile operators and is TCPA / data protection compliant.
(KYC Match):
When a first-time user visits a car rental website, he/she leaves his details which include the mobile number, name, contact details, address etc. The user is verified by the telco. The car rental company receives information about the user and matches the user information provided to the information with the telco. The scores are allotted to each parameter. For example,
- Name Match 10/10
- Surname Match 9/10
- Address Match 10/10
- Email Match 10/10
Based on the logic defined by the car rental company, the account is successfully created.
One step authentication:
Another example would be of a digital payment company that initiates a ‘Pop Up’ for prompting the user to fill his/her telecom details. When the user selects the “Connect to telco” option, it is considered as consent. The user enters their mobile number and clicks ‘continue’ which is once again considered as explicit consent. The user is then shown the details captured by the telco and prompted to continue. The user details are automatically displayed in the form which enables the user to sign in securely within a few seconds without manually entering all details, thus eliminating errors.
Service providers are at an edge where their user experience can make or break their business. They are also in need to escalate experience to retain the customers. Optimisations, such as implementing mobile servers will nowhere come close to implementing mobile identity solutions which provide an instant login and registration.